Why We Built Identity Runtime Attribution for AI Agents
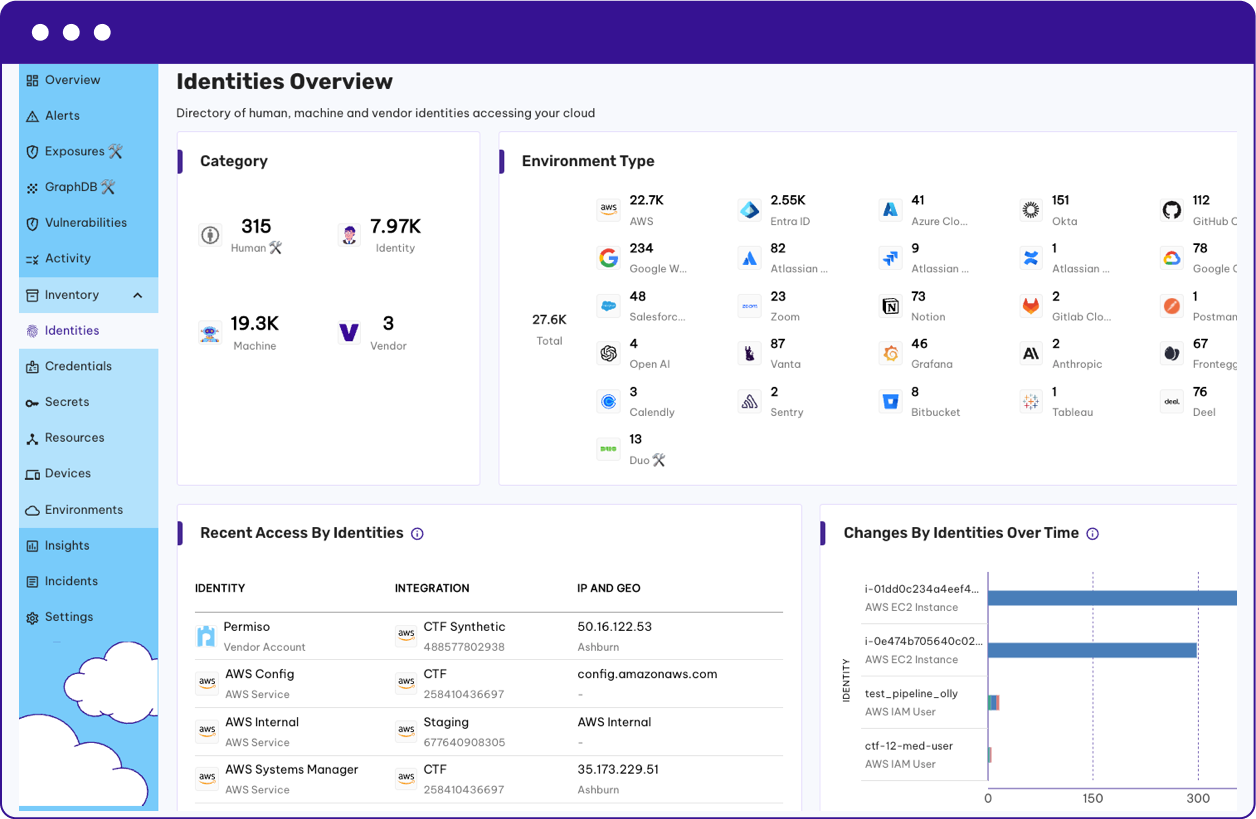
What happens when an agent hits a hard permission constraint on a task it's been told to complete? Sometimes it reasons its way around it. We watched a coding agent bypass GitHub repo permissions by finding a different path to clone and merge the code it needed because non-deterministic systems take paths you cannot anticipate. The real gap in agent security is what happens after authentication, where IdPs go blind to every tool call, MCP invocation, and sub-agent spawn.
What happens when an agent hits a hard permission constraint on a task it's been told to complete? Sometimes it reasons its way around it. We watched a coding agent bypass GitHub repo permissions by finding a different path to clone and merge the code it needed because non-deterministic systems take paths you cannot anticipate. The real gap in agent security is what happens after authentication, where IdPs go blind to every tool call, MCP invocation, and sub-agent spawn.
Read More



.png)





.png?width=110&height=136&name=SIREN_01%201%20(1).png)





.png)